Cloud Architecture
Scalable & Secure Cloud Architecture
Design highly available, fault-tolerant, and secure cloud systems that scale with your business needs. Our expert architects build resilient infrastructure for mission-critical applications.
Get Started →
Cloud Architecture Diagram
Why This Architecture?
⚡ High Availability
Multiple services and load balancing ensure zero downtime with automatic failover and redundancy across multiple availability zones.
📈 Scalability
Auto-scaling handles traffic growth without performance loss. Scale horizontally and vertically based on demand patterns.
🔒 Security
Network isolation, IAM, encryption, and monitoring protect your data with enterprise-grade security at every layer.
Key Architecture Components
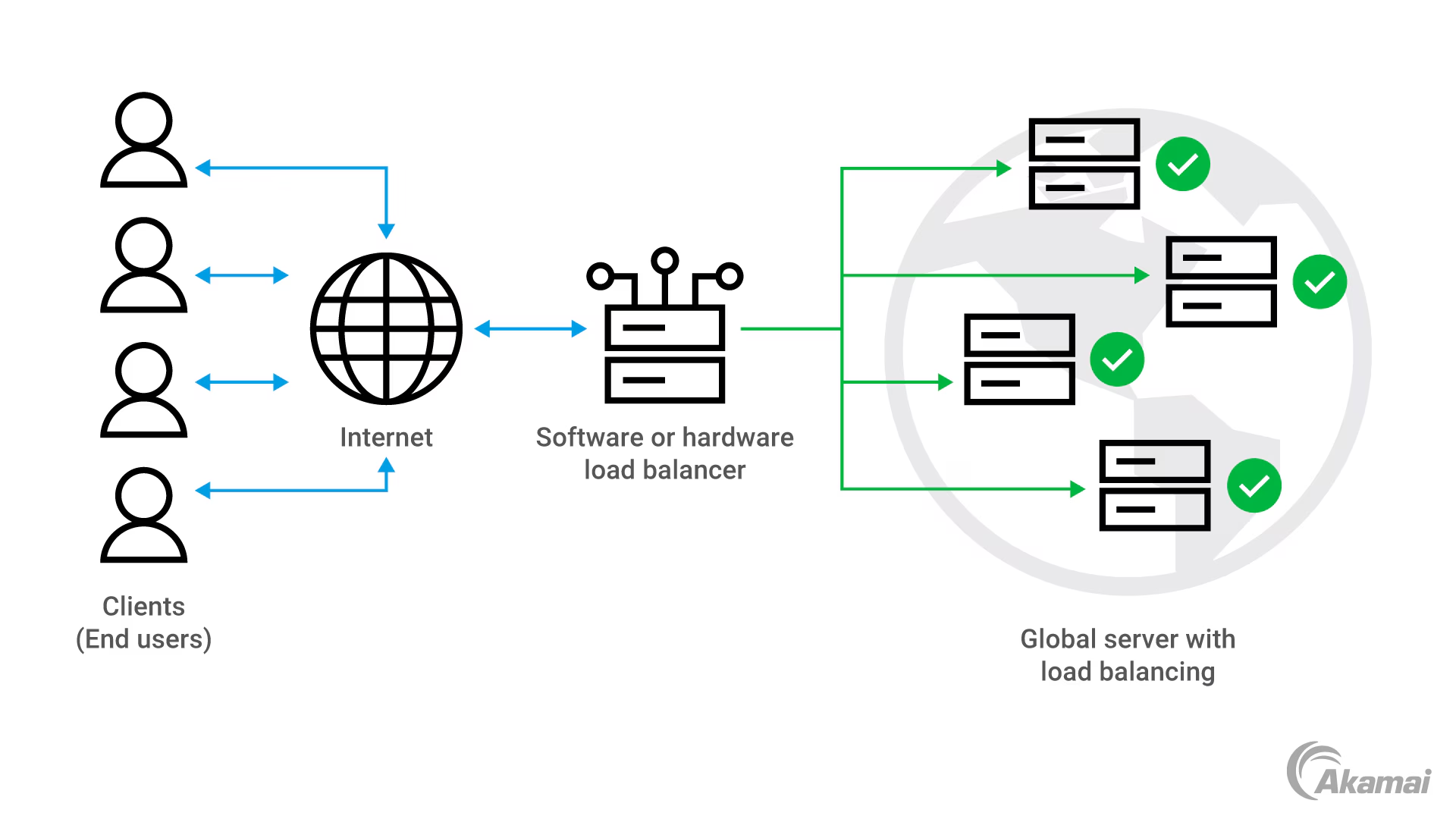
🌐 Global Load Balancing
Distribute traffic intelligently across multiple servers and regions. Our load balancing solution ensures optimal performance by routing requests to the nearest available server, reducing latency and improving user experience worldwide.
- Health check monitoring
- SSL/TLS termination
- Geographic routing
- Auto-failover capability
- Traffic shaping
- DDoS protection
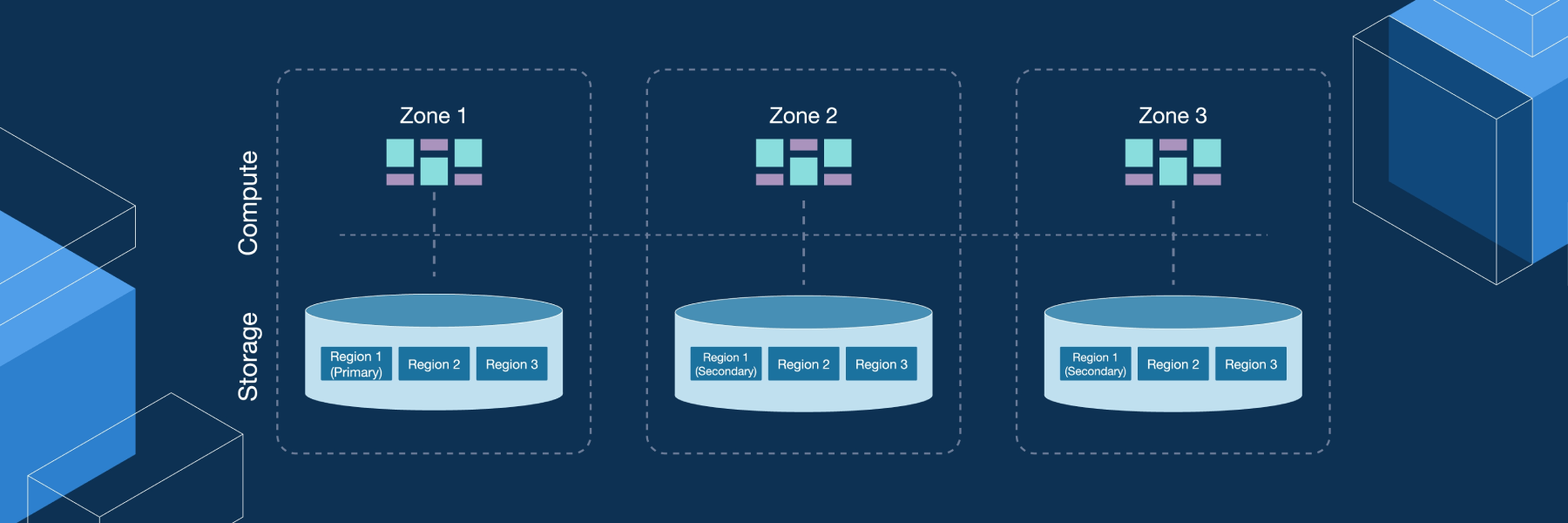
💾 Distributed Database Architecture
Multi-region database replication with automatic backup and recovery. Our database layer supports both SQL and NoSQL workloads with built-in redundancy, ensuring your data is always available and protected.
- Multi-AZ deployment
- Automatic backups
- Read replicas
- Point-in-time recovery
- Cross-region replication
- Performance monitoring
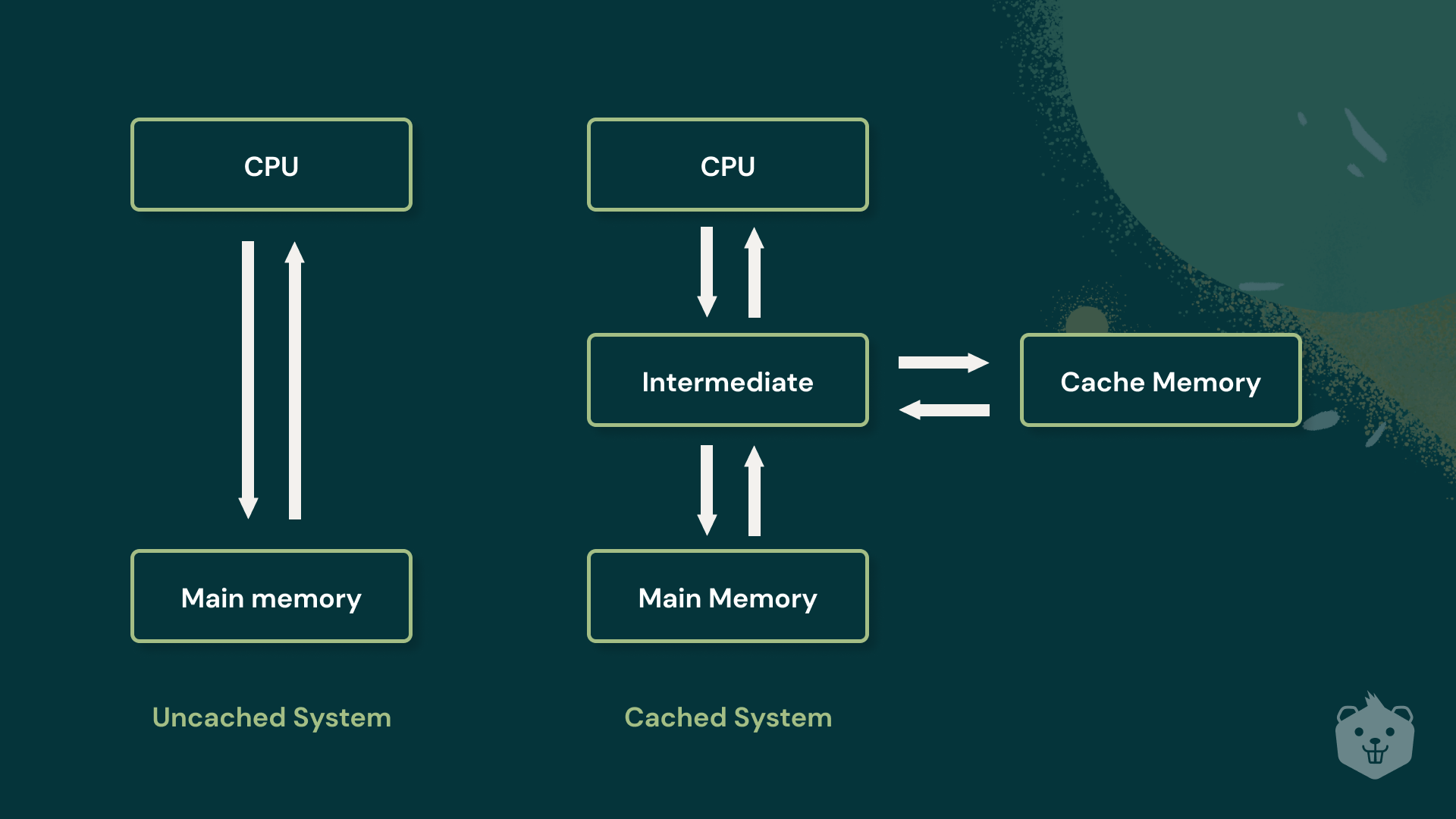
⚡ High-Performance Caching
In-memory caching layer that dramatically reduces database load and improves response times. Our caching strategy uses Redis and CDN integration to serve content faster to users around the globe.
- Distributed cache clusters
- CDN integration
- Cache invalidation strategies
- Session management
- Edge caching
- Real-time analytics
Architecture by the Numbers
Enterprise-Grade Security
DDoS Protection
Multi-layer defense against distributed denial of service attacks with automatic mitigation and real-time threat intelligence.
End-to-End Encryption
All data encrypted in transit and at rest using industry-standard AES-256 encryption with key management.
24/7 Monitoring
Real-time threat detection and automated incident response across all infrastructure with comprehensive logging.
Compliance
SOC 2, ISO 27001, GDPR, and HIPAA compliant infrastructure and processes with regular audits and reporting.
